Protecting Against Cybercrime
What is Cybercrime?
Cybercrime refers to any criminal activity conducted over the Internet – Cyber criminals use sophisticated methods to illegally obtain your personal or business’ confidential information, such as financial documents. Cybercrime falls into two main categories: phishing attacks and computer viruses.
Phishing attacks generally include authentic looking emails that are sent from seemingly legitimate businesses that direct users to fraudulent websites and instruct them to log in, thereby capturing their usernames and passwords in order to gain access to their accounts. Computer viruses are software programs that corrupt your computer data and are activated by opening unfamiliar attachments or links in your email (often from senders in your address book).
How to Protect Yourself and Your Business from Cybercrime?
Preventing online fraud starts with you. Learning to spot and avoid online scams is your best defense against cybercrime.
Protect Yourself From Phishing Attacks
- Turn on your email spam filter to prevent most phishing emails from reaching your inbox.
- Protect your computer, server and network with antivirus software.
- Don’t open emails from people you don’t know.
- Don’t click on links in suspicious looking emails.
- Check for spelling and grammatical errors. Often times, phishing emails originate from foreign countries where English may not be commonly used. Sometimes, these errors are intentionally included to make it easier for these emails to bypass spam filters.
- Check that a website is secure by looking for a “lock” image in the browser window.
- Check that a website is secure by confirming that the URL starts with https:// instead of http://.
- Instead of following the instructions in the email, call the company’s customer service to verify the information request.
Protect Yourself From Computer Viruses
- Install antivirus software and a firewall.
- Ensure that you’re using the most up-to-date antivirus software version.
- Don’t open email attachments or click on links from people you don’t know, or attachments or links that look suspicious from people in your address book.
Finally, familiarize yourself with the common red flags associated with phishing attacks and computer viruses. These include urgent requests for money (often for package delivery), links to misspelled websites (for example, storedotcom.com) and certificate errors or lack of SSL for websites.
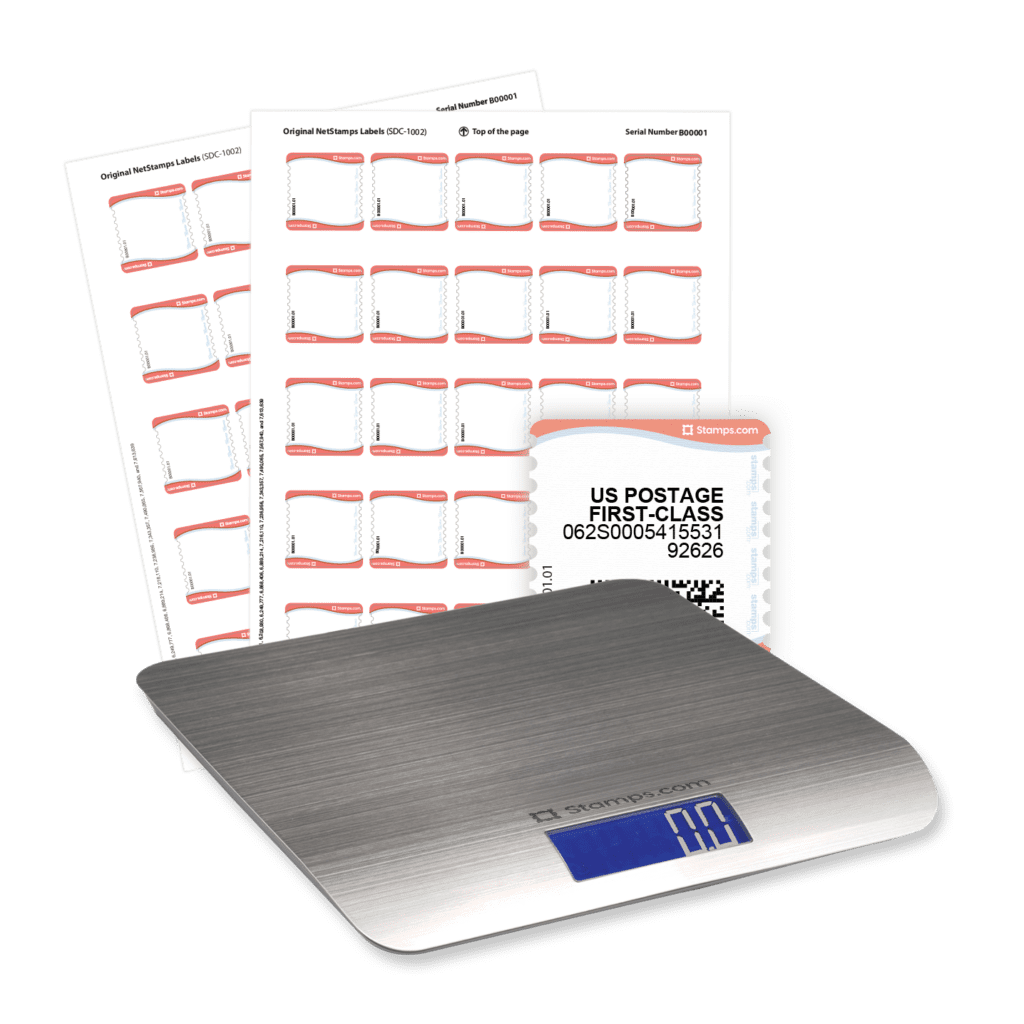
Perks of your risk-free trial
- Free mailing supplies
- Free 5 lb digital scale
- Free scheduled pickups
- No contract, cancel any time